Understanding the Trezor Wallet Login process can help users protect their digital assets while enjoying smooth and secure account access.
This guide explains everything about Trezor Wallet Login, its benefits, security features, and tips to keep your crypto wallet protected.
Why Trezor Wallet Login Matters for Crypto Security
Unlike traditional online wallets, Trezor hardware wallets store your private keys offline. This means hackers cannot easily access your funds through internet-based attacks. The Trezor Wallet Login process is designed to ensure only the wallet owner can approve transactions and manage assets.
When users log in through the Trezor ecosystem, they gain a secure gateway to send, receive, and monitor cryptocurrencies without exposing sensitive data.
How to Access Trezor Wallet Login Securely
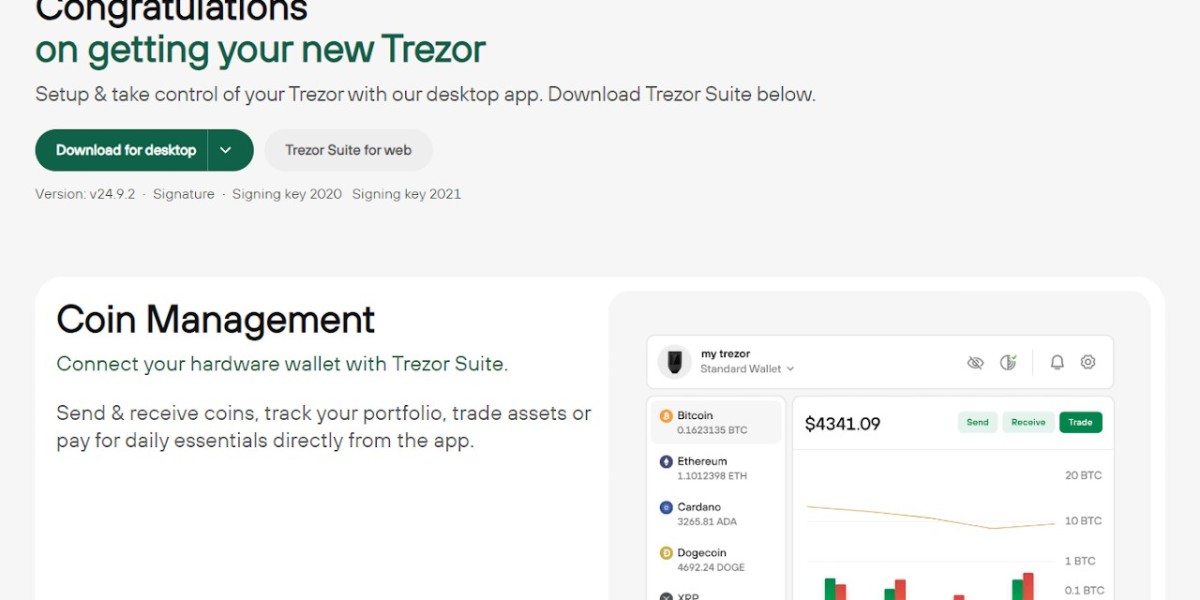
To begin using your Trezor wallet, users typically connect their hardware device to a computer or mobile device and access the official Trezor platform.
Follow These Basic Steps:
- Connect your Trezor hardware wallet to your device.
- Open the official Trezor Suite application or web interface.
- Enter your PIN code securely on the device.
- Confirm authentication through your hardware wallet.
- Access your crypto portfolio safely.
This login method provides an additional layer of security because authentication happens directly on the physical device rather than online servers.
Powerful Security Features of Trezor Wallet Login
Offline Private Key Protection
Your private keys never leave the Trezor hardware wallet. This significantly reduces exposure to phishing attacks and malware.
PIN and Passphrase Security
Trezor allows users to create a unique PIN and optional passphrase for enhanced protection during the login process.
Transaction Verification
Every transaction must be confirmed physically on the device, ensuring unauthorized transfers cannot occur remotely.
Recovery Seed Backup
During setup, users receive a recovery seed phrase that can restore wallet access if the device is lost or damaged.
Open-Source Transparency
The Trezor ecosystem uses open-source technology, allowing developers and security experts to audit its code for vulnerabilities.
Key Benefits of Using Trezor Wallet Login
Enhanced Asset Protection
Trezor helps secure cryptocurrencies against online threats and unauthorized access attempts.
User-Friendly Interface
The Trezor Suite dashboard offers a clean and intuitive experience suitable for both beginners and experienced traders.
Support for Multiple Cryptocurrencies
Users can manage Bitcoin, Ethereum, and thousands of supported digital assets within one secure platform.
Reliable Backup and Recovery
Even if the hardware wallet is lost, users can recover funds using the recovery phrase.
Seamless Portfolio Management
The login system allows easy monitoring of balances, transactions, and account activity.
Tips to Keep Your Trezor Wallet Login Safe
Always Use Official Platforms
Only access Trezor services through official websites and applications to avoid phishing scams.
Protect Your Recovery Phrase
Never share your recovery seed with anyone. Store it securely offline in multiple safe locations.
Enable Additional Passphrase Protection
A strong passphrase adds another layer of security beyond the PIN code.
Keep Firmware Updated
Regular firmware updates improve device performance and strengthen security measures.
Avoid Public Computers
Never log into your Trezor wallet using shared or untrusted devices.
Common Issues During Trezor Wallet Login
Some users may occasionally face login-related issues. Here are a few common problems and solutions:
| Issue | Solution |
|---|---|
| Device not detected | Reconnect USB cable or restart Trezor Suite |
| Incorrect PIN | Carefully enter the correct PIN |
| Firmware outdated | Install the latest firmware update |
| Browser compatibility issue | Use supported browsers or Trezor Suite app |
| Connection errors | Check internet and device permissions |
Frequently Asked Questions (FAQs)
What is Trezor Wallet Login?
Trezor Wallet Login is the secure authentication process used to access and manage cryptocurrency assets through a Trezor hardware wallet.
Is Trezor Wallet Login safe?
Yes, Trezor is considered highly secure because it stores private keys offline and requires physical transaction approval.
Can I recover my wallet if I lose my device?
Yes, users can recover their wallet using the recovery seed phrase provided during setup.
Does Trezor support multiple cryptocurrencies?
Yes, Trezor supports thousands of cryptocurrencies, including Bitcoin, Ethereum, Litecoin, and many ERC-20 tokens.
Do I need internet access for Trezor Wallet Login?
Internet access is needed to interact with blockchain networks, but your private keys remain offline inside the hardware wallet.
Conclusion
The Trezor Wallet Login process offers one of the safest ways to access and manage digital assets. With offline private key storage, PIN protection, passphrase security, and transaction verification, Trezor continues to be a trusted solution for crypto holders worldwide.
Whether you are a beginner entering the crypto market or an experienced investor managing a diverse portfolio, Trezor provides strong protection and a user-friendly experience. By following proper security practices and using official tools, users can confidently safeguard their cryptocurrency investments for the long term.